Networking Assignment: Designing Topology For Sub-Network ConnectionsTo Los Angeles office
Question
Task:
This networking assignment will allow students to demonstrate a Network design based on a real time scenario.
Students must demonstrate their understanding of critical thinking in an IT context by examining given problems and proposing solutions using the methods explored in the unit.
Students will choose a solution, then implement and evaluate their solution.
Approximate word length is upto 1500 words with topology diagrams. The report should be presented with supporting material as appendices such as the calculations for the IP addressing scheme.
Practical assignment brief:
After Covid-19, Hollywood film company was very keen to design and deploy new studio offices to their network that will span four cities in Australia:
Sydney Studio (10000 users)
Melbourne Studio (8000 users)
Brisbane Studio (6000 users)
Gold Coast studio (4700 users)
The company uses 176.XY.0.0/16 at the company headquarters in Los Angeles with 50000 users and needs to use a subnetting structure to incorporate the new cities. Adhering to the subnetting scheme and using VLSM, assign a subnet address to the networks and their links. Each branch’s offices have 8 levels of building and access to the internet is crucial for each office, as well as inter-branch-office networking. Each branch has 6 servers which are located on the Fifth floor of each branch. The large company headquarter is in Los Angeles and the new subnets must have connectivity from Los Angeles and other cities in Australia. You need to think about cost-effectiveness and also Hollywood company is aiming to create an INTRANET for its branches in Australia and USA. You need to think about creating a VPN for this company. Recently two branches in Australia were impacted by phishing attacks and also ransomware attacks. Some new movies that are supposed to be released this Christmas were postponed because of a ransomware attack. Find some solutions to mitigate these types of attacks in future.
Elements:
Your goal is to design, deploy and successfully implement their business requirements. You need to find the best option for your design with consideration of cost-effectiveness and also by using all related network components.
Solution:
You are required to design the topology for the four new sub-networks and their connection to the Los Angeles office. You must document each step you have taken, including your research sources.
You need to come up with a design report and send it to your technical manager.
Report: The report must contain the following sections:
1. Introduction: Critical analysis of networking requirements
2. Local Area Network (LAN): Design and description of Local Area Network for all subnets which must include:
a. Network topology: Discuss the reasons for choosing the particular network topology.
b. LAN design connections to the servers, connection to other subnets and also the internet/intranet, you need to add your design in your report.
3. Hardware: Provide a complete description of all interconnecting devices (switches, routers, hubs and access points) and wiring used to build the network.
Answer
Introduction
“Network design” has been referred to as the arrangement of implementations according to the“computer network infrastructure”. The network design focused in the networking assignmenthas been developed by “network designers”, “engineers”, “IT administrators” as well as other related employees. However, this “network design” has been done before the development according to this “network infrastructure”.
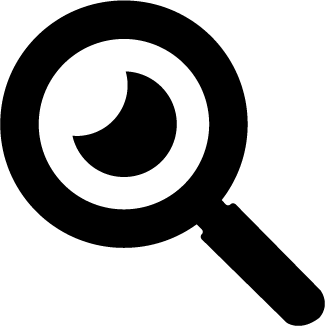
Network topology
A “Network Topology” has been considered as the arrangement with “computer systems” otherwise, “network devices”. As opined that Christiansen et al. (2020), those network devices have been connected to each other. According to this case study, this “network topology” has been considered as a “tree topology”. This tree topology has been considered as a special kind of structure. This structure has been connected with many systems such as the branches of a tree.
Figure 1: Network topology
(Source: Self-Created)
As per the above figure, it has been shown that the router of Australia has many branches like a tree such as Sydney studio, Melbourne studio, Brisbane studio, as well as Gold coast studio. Along with that, Sydney studio has 10000 users and 6 servers. Moreover, Melbourne studio has 8000 users and 6 servers. Along with that, the branches of Brisbane studio have been considered as 6000 users with 6 servers. Moreover, the Gold coast studio branch has been contained with 4700 users as well as 6 servers.
LAN design
“Hierarchical network design” has been involved in dividing this “network” into individual layers. Along with that, Pan et al. (2019) have opined that each layer has been provided with specific functions. Those functions have been defined as their role within the overall network. Moreover, it has been separated into different kinds of functions. Based on this existing network, this “network design” has been considered as “modular,”. This modular has been facilitated with “scalability” as well as “performance”.
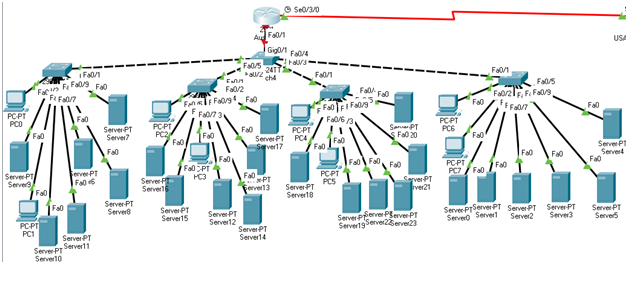
Figure 2: LAN Design
(Source: Self-created)
According to the above figure, it has been considered as the LAN design of this network. This LAN connection has been communicated with each switch and established communication.
IP addressing
According to the case study, it has been mentioned that the company has been used to the range of class B IP addresses such as 176.xy.0.0/16.
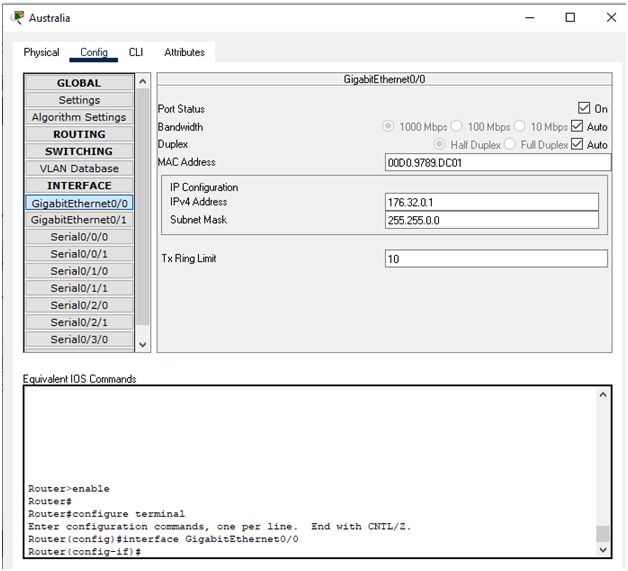
Figure 3: IP address of router of Australia
(Source: Self-created)
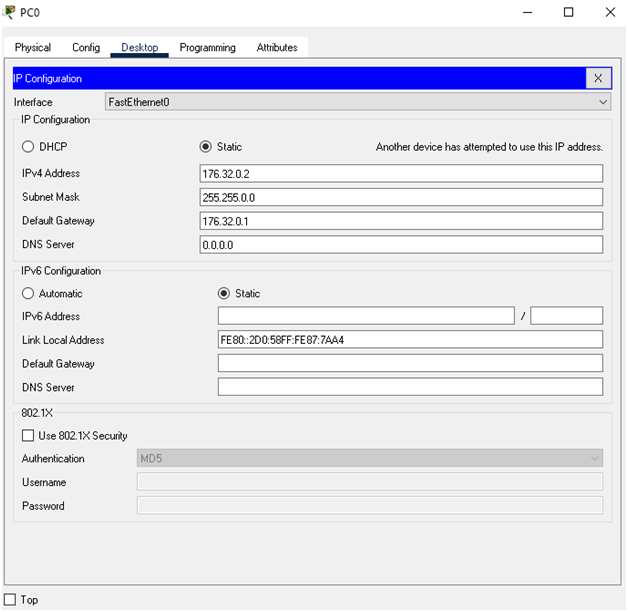
Figure 4: Range of IP address switch 1
(Source: Self-created)
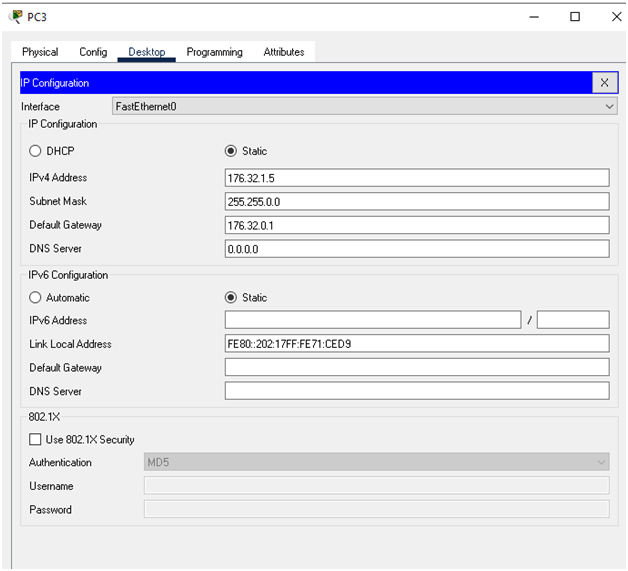
Figure 5: Range of IP address switch 2
(Source: Self-created)
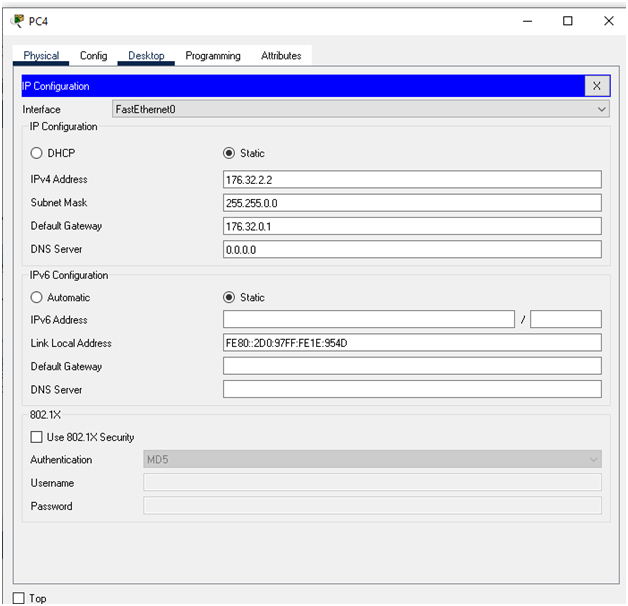
Figure 6: Range of IP address switch 3
(Source: Self-created)
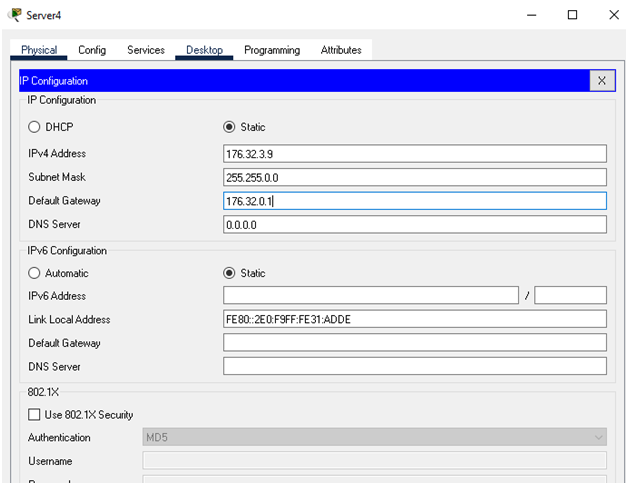
Figure 7: range of IP address switch 4
(Source: Self-created)
According to the above figure, it has been highlighted that the IP address of Australia's router. The IP address of this router is 176.32.0.1 and 255.255.0.0. Along with that, Yuan et al. (2020) have narrated that the router of this network has four switches; the 1st switch of Sydney has been connected with a 176.32.0.1 range of IP addresses. Along with that, the switch of Melbourne Studio has been communicated with the 176.32.1.0 range of IP addresses.
Addressing network security issues and research
There is address network security has been considered as “Native VLAN mismatch”. It has been posted as a “security risk” as well as it has been created as “unintended results”. On the other hand, another issue has been considered as “Trunk mode mismatch”. It has been caused a loss of “network connectivity”. Moreover, the next issue of this network has been allowed “VLANs on trunks”. It has been caused as “unexpected traffic” otherwise; no traffic is to be sent through this trunk.
Hardware
This network diagram has been considered as server, routers. End devices such as PC and last of all switches. Along with that, Vdovjak et al. (2020) have described that a router of this network diagram has been received as well as sending data on “computer networks”. Furthermore, both routers have been combined as the functions of these components. It has been connected with these devices such as switches. Moreover, it has been improved this “business networks”. On the other hand, switches of “network infrastructure” has been considered as “devices operating” at “layer 2” otherwise, the “data link layer” of the “OSI model”. Those connecting devices in this network have been used as packet switching for sending, receiving otherwise, forwarding “data packets” otherwise, “data frames” through this network. According to the switch, it has many ports, computers of these devices have been plugged in. Along with that, “End devices” have been considered as “node devices”. It has been served as a “source point” as well as a “destination point” in the communication. This communication has occurred on this “computer network”. Furthermore, those servers of this network infrastructure have been considered as systems. This system has been provided as “resources, data, services, or programs” that are considered as other computers. Those computers have been known as clients through this network.
Conclusion
According to this case study, it has been concluded that this “network design” has been done before the development according to this “network infrastructure”. This network diagram has been considered as server, routers. End devices such as PC and last of all switches. It has been mentioned that the company has been used to the range of class B IP addresses such as 176.xy.0.0/16.
Reference
Christiansen, M., Hellsten, E., Pisinger, D., Sacramento, D. and Vilhelmsen, C., 2020.Liner shipping network design. European Journal of Operational Research, 286(1), pp.1-20.
Pan, H., Li, F., Liu, Y., Zhang, Q., Wang, M., Lan, S., Zheng, Y., Ma, J., Gu, L., Shen, Y. and Yu, P., 2019. Ultrahigh–energy density lead-free dielectric films via polymorphic nanodomain design. Science, 365(6453), pp.578-582.
Vdovjak, K., Balen, J. and Nenadi, K., 2020. Experimental Evaluation of Desktop Operating Systems Networking Performance.Networking assignment International journal of electrical and computer engineering systems, 11(2), pp.67-76.
Yuan, C., Du, J., Yue, M. and Ma, T., 2020.The design of large scale IP address and port scanning tool. Sensors, 20(16), p.4423.