Networking Assignment: Network Protocols, SDLC & ITSM
Question
Task:
This networking assignment consists of two questions. The first one looks into networking protocol, concepts and standards. The second question looks at SDLC and ITSM.
Question 1: Networking protocols, concepts, and standards
- Show the calculations for finding the estimated percentages of overhead for TCP/IP protocol for IPv4 and IPv6 versions.
- Compare and contrast the IPv4 and the IPv6 header fields. Do they have any fields in common?
- Why is the length of a TCP segment limited to 65,536 bytes?
Question 2: SDLC and ITSM
- What new ITSM trends and technologies are surfacing?
- Discuss the roles and responsibilities of Incident Manager and Change Manager in ITSM.
- How does the Spiral model overcome the limitation of the Waterfall cycle model and the V-shaped cycle model?
- Compare and contrast the Waterfall and V-Model of SDLC. Present two cases where each of the models will be best suited.
Answer
Networking Assignment Question 1: Networking protocols, concepts, and standards
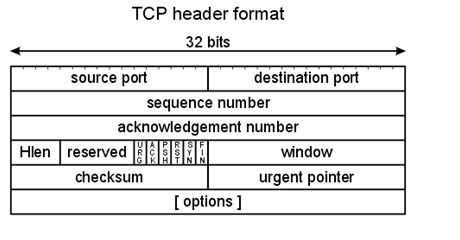
- The TCP header for IPv4 is 20 to 60 Bytes and for IPv6 is 40 Bytes.
The maximum segment size in TCP (MSS) is 1460 Bytes.
Let assume that X Bytes of data is
The number of packets required are X / 1460, rounded to the floor of the result + 1.
For IPv6, the header size is 40 Bytes. Total 40*(X/1460) for all the packets.
Percentage of header = (40 * (X/1460))/X = 40/1460.
Which is approx to 2.8%.
For IPv4, the header size is 20 to 60 Bytes. Total 20*(X/1460) to 60*(X/1460) for all the packets.
Percentage of header = (20 * (X/1460))/X to (60 * (X/1460))/X = 20/1460 to 60/1460.
Which is approx to 1.3% to 4.1%.
-
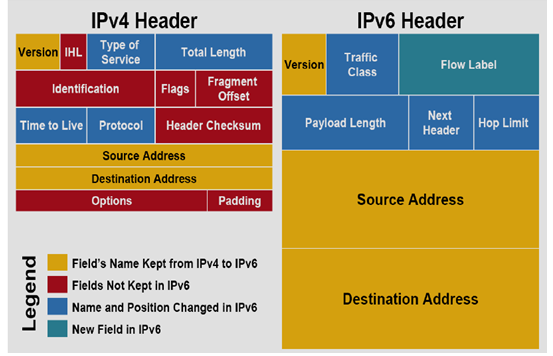
IPv4 uses a 32-bit address while IPv6 uses a 128-bit address. IPv6 has more flexibility in terms of auto and renumbering of address configuration, end-to-end integrity, large space for address allocation, security features, encryption and authentication. While in IPv4 there are some features like availability of checksum, also support manual and DHCP address configuration.
In IPv6 there is no optional header (it had extensions) while in others there is an optional header.
The common field in both these internet protocols are Version field, Source address Destination address, however these do differ in size.
- The window field in the TCP header is 16 bits. Window field is the number of bytes that the receiver can accept. The maximum size that can be represented in 16 bits is 1111 1111 1111 1111, which is equal to 2^16-1 bytes which is equal to 65535. Hence the size is limited to 65536, it cannot exceed 65535 bytes.
Question 2: SDLC and ITSM
- The new ITSM trends that are surfacing are:
- AI Adoption: Planning of AI is being implemented to ensure effectiveness and ease use, and much precise functionality. Many new features which can be added using AI are smart chat bots, intelligence and AI-assisted data analysis.
- Automation Exploitation: Automation can be used to improve upon the following fields:- increasing speed, reducing cost, improving quality. The IT department which is overworked and not funded well will have a positive effect upon implementation of automation.
- ESM Adoption: Enterprise Service Management is a method in which the management system is well addressed and makes them understand the need, so that the employees are trained best to support all their customers.
- Digital Transformation: Yes, this is something which can be applied to the IT department to improve products, services and revenue streams. Using technology and data one can improve customer engagement.
-
Role of Incident Manager: After occurrence of any incident, managing and planning the process by which they can restore operation as quickly, effectively.
Few Responsibilities of Incident Manager:
- Planning activities which are needed to perform. Monitoring all the process and reporting on the process.
- Frequently communicate with Incident Process Owners.
- Is the point of contact for all major Decision/Incidents?
- Monitoring the workloads and incidents to ensure that other agreements are ensured.
- Ensuring and checking for all the closure of all resolved records by confirming from the end-user, also providing guidance to the Other Incident Coordinators.
Role of Change Manager:At the time of Changes, ensuring and operating all the discussed and planned process, planning the efficiency of process and process audits. Also, manage the cycle for proper improvement.
Few Responsibilities of Change Manager:
- Managing all the activities necessary to track and control the Changes in environment.
- Ensuring that all the process and status are communicated to the proper associated groups.
- Scheduling the meetings which are urgent with CAB whenever necessary.
- Producing the management report and reporting to upper management teams/managers.
- Leading and responsible for assigning the work to the staff members based upon their adequate skills/levels.
- The limitations of Waterfall cycle models are:
- No working of the software can be produced until the late cycles.
- Poor model for long projects, complex and object-oriented projects.
- No accommodation for changing requirements.
- Cannot identify the bottleneck and other challenges in the early cycles.
The limitations of V-shaped cycle models are:
- It is uncertain and highly risky.
- Again poor model for long projects, complex and object-oriented projects.
- No working of the software can be produced until the late cycles.
- The functionality cannot be changed once the process is in testing models.
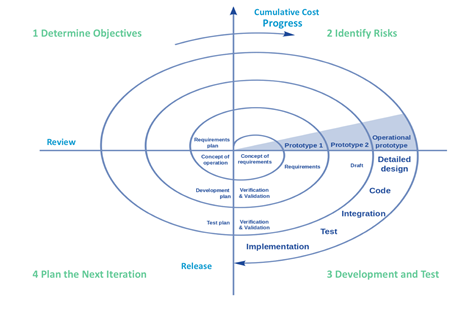
In the Spiral model, which does not sequential stages(follows evolutionary method) like the Waterfall model, decreases the risk as the error can be identified at early stages. It can also be used in large projects. In this method one has flexibility of change which is not present in both V-model and Waterfall model. The life cycle in the Spiral model is divided into smaller parts. Whenever there are any parts which have higher risk, that are performed first so they can be rectified at an earlier stage. Developers can create an earlier working prototype so that the users can point out the flaws. There can be significant changes in the product during the development phase. It is preferred when the customers are not sure of their requirements.
- The limitations of both the models are mentioned above.
When to use Waterfall cycle models:
- There are no ambiguous requirements and the product definition is fixed. No major changes in the future.
- All the requirements are well documented and clear to the developers and the project is short.
- When the number of defects are needed to be low. Softwares made by V-model has a higher number of defects.
When to use V shaped cycle model:
- Preferred when there are continuous changes that need to be included.
- When you have a budget constraint. The changes in the V-model are cheap to implement as testing and development are done simultaneously.
References
[1] Comparison between IPv4 Header and IPv6 Header. Omnisecu.com. (2020). Retrieved 9 May 2020, from https://www.omnisecu.com/tcpip/ipv6/comparison-between-ipv4-header-and-ipv6-header.php.
[2] Comparison between IPv4 Header and IPv6 Header. Omnisecu.com. (2020). Retrieved 9 May 2020, from https://www.omnisecu.com/tcpip/ipv6/comparison-between-ipv4-header-and-ipv6-header.php.
[3] TCP Header. Telescript.denayer.wenk.be. (2020). Networking assignment
Retrieved 9 May 2020, from http://telescript.denayer.wenk.be/~hcr/cn/idoceo/tcp_header.html.
[4] IT Service Management. Smcc.emory.edu. (2020). Retrieved 9 May 2020, from http://smcc.emory.edu/itsm_process/.
[5] SDLC - Waterfall Model - Tutorialspoint. Tutorialspoint.com. (2020). Retrieved 9 May 2020, from https://www.tutorialspoint.com/sdlc/sdlc_waterfall_model.htm.
[6] Existek.com. (2020). Retrieved 9 May 2020, from https://existek.com/blog/sdlc-models/.